Introduction
Agar aap cyber security, ethical hacking ya web development field me enter karna chahte ho, to ek term aapko baar-baar sunne ko milegi — OWASP Top 10.
Web applications aaj har jagah use ho rahi hain:
- Online banking
- E-commerce websites
- Government portals
- Social media platforms
- Healthcare systems
Jahan web application hai, wahan security risk bhi hai.
Har saal duniya bhar me lakhon websites hack hoti hain. Inme se zyada tar attacks kisi advanced unknown technique se nahi, balki common web vulnerabilities ki wajah se hote hain.
Isi liye OWASP Top 10 banaya gaya.
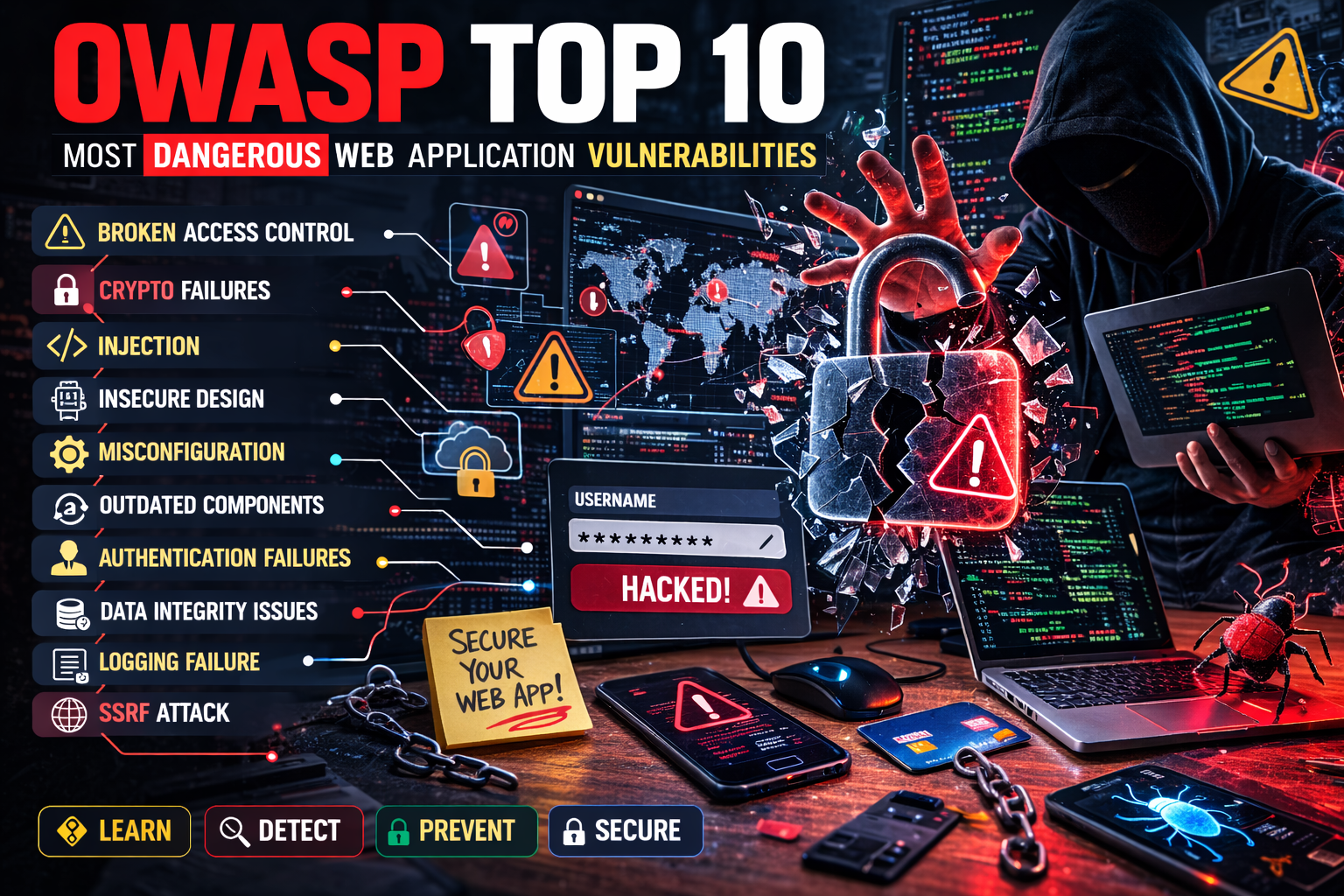
Ye list duniya ki sabse common aur dangerous web application vulnerabilities ko highlight karti hai.
Agar aap:
- Ethical hacker banna chahte ho
- Bug bounty start karna chahte ho
- Developer ho
- Security analyst banna chahte ho
To OWASP Top 10 samajhna mandatory hai.
OWASP Kya Hai?
OWASP ka full form hai:
Open Web Application Security Project
Ye ek non-profit organization hai jo web security ko improve karne ke liye free resources provide karti hai.
OWASP provide karta hai:
- Security documentation
- Testing guides
- Free tools
- Top 10 vulnerability list
- Developer guidelines
OWASP ka mission hai:
Secure software development ko promote karna.
OWASP Top 10 Kya Hai?
OWASP Top 10 ek curated list hai jisme web applications ki 10 sabse critical security risks bataye jaate hain.
Ye list:
- Real-world data breaches ke analysis par based hoti hai
- Security experts ke research par based hoti hai
- Har kuch saalon me update hoti hai
Ye ranking nahi hoti, balki risk categories hoti hain.
Iska purpose hai:
- Awareness create karna
- Developers ko guide dena
- Organizations ko risk samjhana
- Security professionals ko testing roadmap dena
OWASP Top 10 – Detailed Explanation
Ab hum har vulnerability ko deep level par samjhenge.
1. Broken Access Control
Ye Kya Hai?
Jab application users ko un resources ka access de deti hai jinka access unhe nahi milna chahiye.
Access control ka matlab hota hai:
- Kaun kya dekh sakta hai
- Kaun kya edit kar sakta hai
- Kaun kya delete kar sakta hai
Agar ye properly implement nahi hota, to Broken Access Control hota hai.
Real Example
Ek website me 2 types ke users hain:
- Normal user
- Admin
Admin panel ka URL hai:
/admin/dashboard
Agar normal user manually ye URL type karke admin dashboard access kar le, to ye broken access control hai.
Advanced Example
User ID parameter change karke doosre user ka data dekhna:
example.com/profile?id=5
Agar id=6 karne se kisi aur ka profile open ho jaye, to vulnerability hai.
Impact
- Data leak
- Account takeover
- Privilege escalation
- Business logic bypass
Prevention
- Role-based access control (RBAC)
- Server-side authorization checks
- Access control testing
- Default deny policy
2. Cryptographic Failures
Pehle iska naam tha: Sensitive Data Exposure
Ye Kya Hai?
Jab sensitive data properly encrypt nahi hota.
Sensitive data examples:
- Passwords
- Credit card numbers
- Aadhaar numbers
- Medical data
Real Example
Website HTTP use kar rahi hai HTTPS ki jagah.
Agar public WiFi par koi packet sniffing kare, to login credentials capture ho sakte hain.
Common Mistakes
- Plain text password store karna
- Weak hashing algorithm use karna
- SSL certificate misconfiguration
Impact
- Identity theft
- Financial fraud
- Data breach
Prevention
- HTTPS enforce karein
- Strong encryption use karein
- Password hashing (bcrypt, Argon2)
- Secure key management
3. Injection
Ye sabse dangerous aur common vulnerability category hai.
Isme aate hain:
- SQL Injection
- Command Injection
- LDAP Injection
- XML Injection
SQL Injection Example
Login query:
SELECT * FROM users WHERE username='$u' AND password='$p';
Attacker input:
admin' OR '1'='1
Result:
Login bypass.
Command Injection Example
Server user input ko system command me use karta hai.
Attacker malicious command inject kar deta hai.
Impact
- Database compromise
- Full server access
- Data manipulation
- Remote code execution
Prevention
- Parameterized queries
- Input validation
- ORM frameworks
- Escaping special characters
4. Insecure Design
Ye coding mistake nahi hoti.
Ye planning aur architecture mistake hoti hai.
Example
- No rate limiting → brute force possible
- No OTP verification → account takeover
- No transaction validation → payment manipulation
Impact
- Business logic abuse
- Fraud
- Account compromise
Prevention
- Threat modeling
- Secure design practices
- Security review phase
- Design validation
5. Security Misconfiguration
Ye bahut common issue hai.
Examples
- Default credentials
- Admin panel publicly accessible
- Debug mode enabled
- Unnecessary services running
Real Scenario
Developer testing ke liye debug mode on karta hai, production me off karna bhool jata hai.
Error messages se database structure leak ho jata hai.
Prevention
- Secure configuration checklist
- Regular patching
- Disable unused services
- Environment separation
6. Vulnerable and Outdated Components
Agar aap outdated software use kar rahe ho, to aap risk me ho.
Example
Old WordPress plugin
Old PHP version
Outdated Apache server
Attackers known vulnerabilities exploit kar sakte hain.
Prevention
- Regular updates
- Patch management
- Dependency scanning
- Software inventory maintain karein
7. Identification and Authentication Failures
Jab login system weak hota hai.
Examples
- Weak password allowed
- No account lockout
- No MFA
- Predictable session ID
Impact
- Account takeover
- Brute force attack
- Session hijacking
Prevention
- Strong password policy
- Multi-factor authentication
- Secure session handling
- Rate limiting
8. Software and Data Integrity Failures
Jab application untrusted updates ya code ko blindly accept kar leti hai.
Example
Application automatic update install karta hai bina signature verify kiye.
Attacker malicious update push kar deta hai.
Prevention
- Digital signature verification
- Secure CI/CD pipeline
- Dependency integrity check
9. Security Logging and Monitoring Failures
Agar attack ho raha hai aur system detect hi nahi karta, to problem serious hai.
Example
Repeated failed login attempts ho rahe hain, but koi alert nahi.
Impact
- Late detection
- Bigger damage
- No forensic trail
Prevention
- Centralized logging
- Real-time monitoring
- SIEM integration
- Alert system
10. Server-Side Request Forgery (SSRF)
Modern cloud systems me common vulnerability.
Ye Kya Hai?
Attacker server ko internal resources access karne par majboor karta hai.
Example
Server URL fetch feature use karta hai.
Attacker internal IP access karne ki request bhej deta hai.
Impact
- Internal data leak
- Cloud metadata exposure
- Remote code execution
Prevention
- Input validation
- Whitelist URLs
- Network segmentation
- Disable unnecessary URL fetch
OWASP Top 10 Ka Real Importance
Zyada tar real-world breaches inhi categories me aate hain.
Companies interview me puchti hain:
- SQL Injection kya hai?
- XSS ke types?
- Broken Access Control example?
Agar aapko OWASP Top 10 strong hai, to aap security interview me strong ho.
OWASP Top 10 Aur Bug Bounty
Bug bounty platforms me 70% bugs inhi categories me milte hain.
Agar aap serious ho:
- OWASP documentation padho
- Practice lab me karo
- Reports padho
Beginner Learning Roadmap
- Basic HTML
- HTTP protocol
- SQL basics
- JavaScript basics
- SQL Injection
- XSS
- OWASP Top 10
- Practical testing
Practical Practice Platforms
- DVWA
- OWASP Juice Shop
- Hack The Box
- TryHackMe
Sirf legal lab me practice karein.
Common Beginner Mistakes
- Tools pe focus, concept ignore
- Bina permission testing
- Alert box ko success samajhna
- Prevention skip karna
Conclusion
OWASP Top 10 web security ka foundation hai.
Agar aap ethical hacking, bug bounty ya cyber security me career banana chahte ho, to is list ko deeply samajhna zaroori hai.
Ye sirf attacks ki list nahi hai, balki secure development ka roadmap hai.
Security ka golden rule:
Understand the risk. Prevent the risk.
Important Note
Ye content sirf educational purpose aur cyber security awareness ke liye share kiya gaya hai. Bina permission kisi website ya system par testing karna illegal ho sakta hai.