Nmap kya hai aur kaise use kare? Is beginner guide me Nmap ke features, basic commands aur port scanning ko simple Hindi me samjhein.
Introduction
Agar aap ethical hacking ya cyber security seekh rahe ho, to ek naam aapko baar-baar sunne ko milega — Nmap. Ye ek powerful network scanning tool hai jo beginners se lekar professionals tak sab use karte hain. Cyber security ki duniya me practical knowledge sabse important hoti hai, aur Nmap us practical journey ka ek strong foundation mana jata hai.
Jab bhi aap kisi network ko analyze karna chahte ho — kaun-kaun se devices connected hain, kaun se ports open hain, kaun si services run ho rahi hain — in sab ka jawab Nmap deta hai. Isi wajah se ethical hacking me Nmap ko “must-know tool” kaha jata hai.
Is detailed guide me hum Nmap ko bilkul beginner-friendly language me step-by-step samjhenge. Agar aapne Kali Linux install kar liya hai aur basic terminal commands jante ho, to ye guide aapke liye perfect hai.
Nmap Kya Hai?
Nmap ka full form hai Network Mapper. Ye ek open-source tool hai jo network discovery aur security auditing ke liye design kiya gaya hai.
Simple language me:
Nmap ek aisa tool hai jo network ke andar active devices, unke open ports aur running services ka pata lagata hai.
Ye tool specially design kiya gaya hai:
- Ethical hackers ke liye
- Network administrators ke liye
- Cyber security professionals ke liye
Nmap ki help se aap kisi bhi target system ka “network map” bana sakte ho.
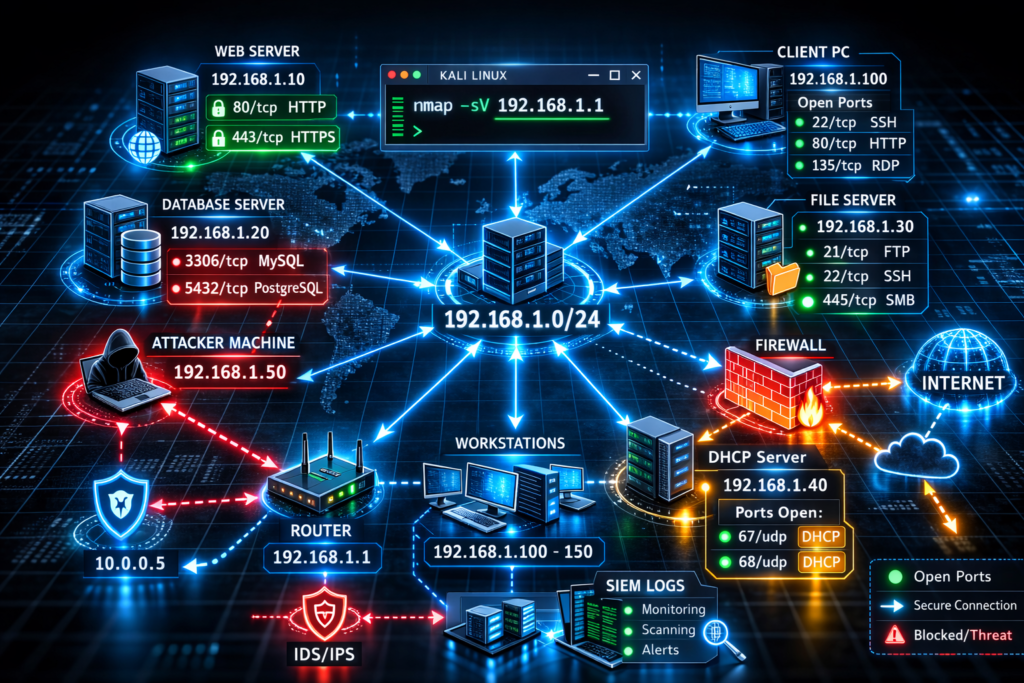
🌐 Network Visualization Samjho (Concept Clear Karein)
Jab Nmap scan karta hai, to basically ye check karta hai:
- Target system online hai ya nahi
- Kaun se ports open hain
- Kaun si service run ho rahi hai
- Kabhi-kabhi OS bhi guess karta hai
Ports ko aap ghar ke darwazon ki tarah samajh sakte ho. Agar darwaza khula hai (open port), to wahan koi service available hai.
Nmap Ka Use Kis Liye Hota Hai?
Nmap sirf ek port scanner nahi hai — ye ek complete reconnaissance tool hai.
Major Uses:
- Network devices discover karna
- Open ports identify karna
- Running services detect karna
- Service versions check karna
- Operating system detect karna
- Security auditing
- Vulnerability assessment ka initial step
Isliye ethical hacking me Nmap ko foundation tool mana jata hai.
Kali Linux Me Nmap Installed Hota Hai?
Agar aap Kali Linux use kar rahe ho, to usually Nmap pre-installed hota hai. Phir bhi confirm karna best practice hota hai.
Check Karne Ki Command:
nmap --version
Agar Installed Hai:
Aapko version information show hogi.
Agar Installed Nahi Hai:
Install karo:
sudo apt update
sudo apt install nmap
Bas, installation ho jayega.
Nmap Ka Basic Syntax
Nmap ka syntax bahut simple hai:
nmap [target]
Yahan target ho sakta hai:
- IP address (192.168.1.1)
- Domain name (example.com)
- Network range (192.168.1.0/24)
Example:
nmap scanme.nmap.org
Ye Nmap ka official test server hai — beginners ke liye safe practice target.
Nmap Se Simple Scan Kaise Kare (Step-by-Step)
Step 1: Terminal Open Kare
Kali Linux me:
- Terminal icon par click karo
ya - Press:
Ctrl + Alt + T
Step 2: Basic Scan Run Kare
nmap scanme.nmap.org
Ye Nmap ka official test server hai – beginners ke liye safe.
Step 3: Output Samjho
Example output line:
22/tcp open ssh
80/tcp open http
Iska matlab:
- 22 → Port number
- tcp → Protocol
- open → Status
- ssh/http → Service name
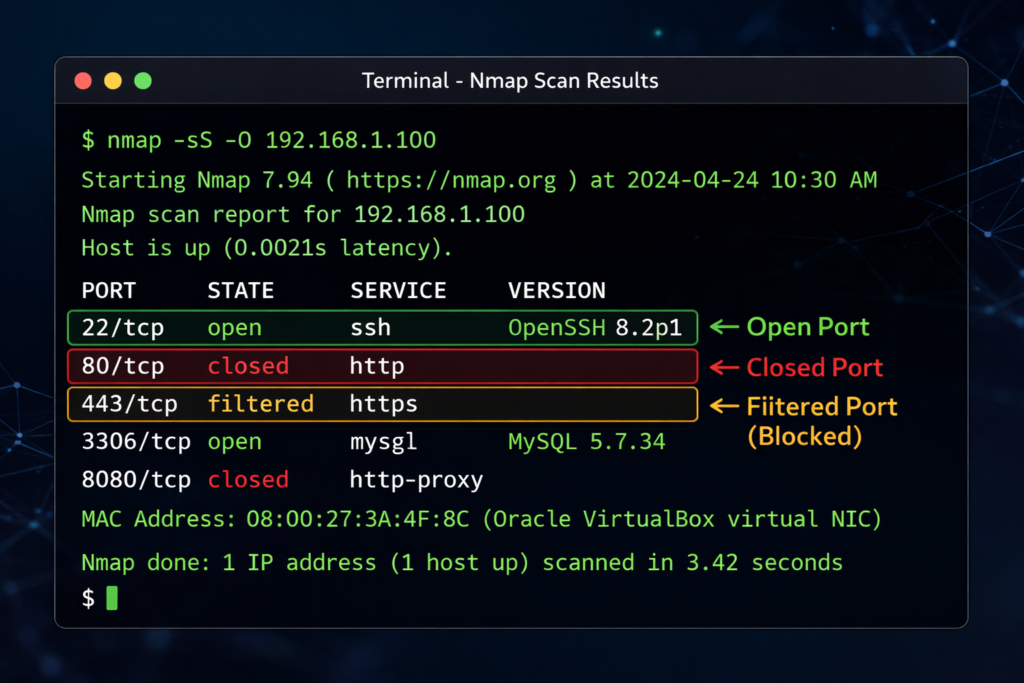
Nmap Output Kaise Samjhe?
Beginners ke liye output samajhna sabse important skill hai.
Important Status Terms:
- open → Port active hai
- closed → Port available nahi
- filtered → Firewall block kar raha hai
Example:
80/tcp open http
Matlab: Port 80 open hai aur HTTP service run ho rahi hai.
Closed vs Filtered Ports Ka Matlab
Jab aap Nmap scan run karte ho, to sirf open ports hi nahi milte. Kabhi-kabhi aapko closed aur filtered bhi dikhta hai.
Closed Port
Closed ka matlab hai ki port accessible hai, lekin koi service run nahi ho rahi.
Example:
80/tcp closed http
Filtered Port
Filtered ka matlab hai firewall ya security device Nmap ke packets ko block kar raha hai.
Example:
80/tcp filtered http
Filtered ports ka matlab hota hai ki system firewall protected ho sakta hai.
Nmap Ke Important Scan Types
Ab thoda advanced level par chalte hain.
Fast Scan (-F)
nmap -F scanme.nmap.org
Ye sirf common ports scan karta hai.
Fast hai, lekin detailed nahi.
TCP SYN Scan (-sS) Kya Hota Hai?
TCP SYN Scan ko Nmap me Half-Open Scan bhi kaha jata hai. Ye Nmap ka sabse popular aur commonly used scan type hai.
Command:
sudo nmap -sS scanme.nmap.org
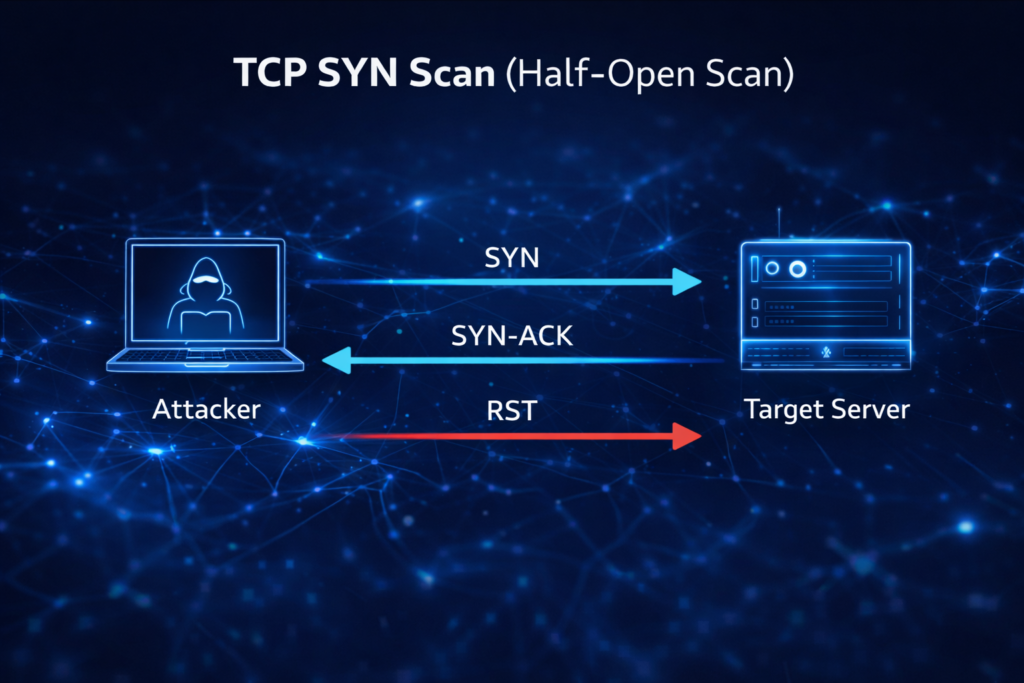
Ye Kaise Kaam Karta Hai?
TCP handshake normally 3 steps me hota hai:
- Client → SYN
- Server → SYN-ACK
- Client → ACK
Lekin SYN scan me Nmap third step complete nahi karta. Agar port open hota hai, to server SYN-ACK bhejta hai aur Nmap turant RST bhej kar connection close kar deta hai.
Isliye ise Half-Open Scan kaha jata hai.
Iske Advantages:
- Fast
- Stealthy
- Reliable
- Most widely used
Agar aap sudo ke sath normal nmap run karte ho, to by default SYN scan hota hai.
TCP Connect Scan (-sT)
Agar aap sudo ke bina nmap run karte ho, to default scan type TCP Connect Scan hota hai.
Command:
nmap -sT scanme.nmap.org
Ye complete TCP handshake karta hai (SYN → SYN-ACK → ACK).
Isliye ye SYN scan se thoda slow hota hai aur easily detect bhi ho sakta hai.
Difference Between -sS and -sT
- -sS = Half-open (stealthy)
- -sT = Full connection
Beginners ke liye pehle -sT samajhna easy hota hai.
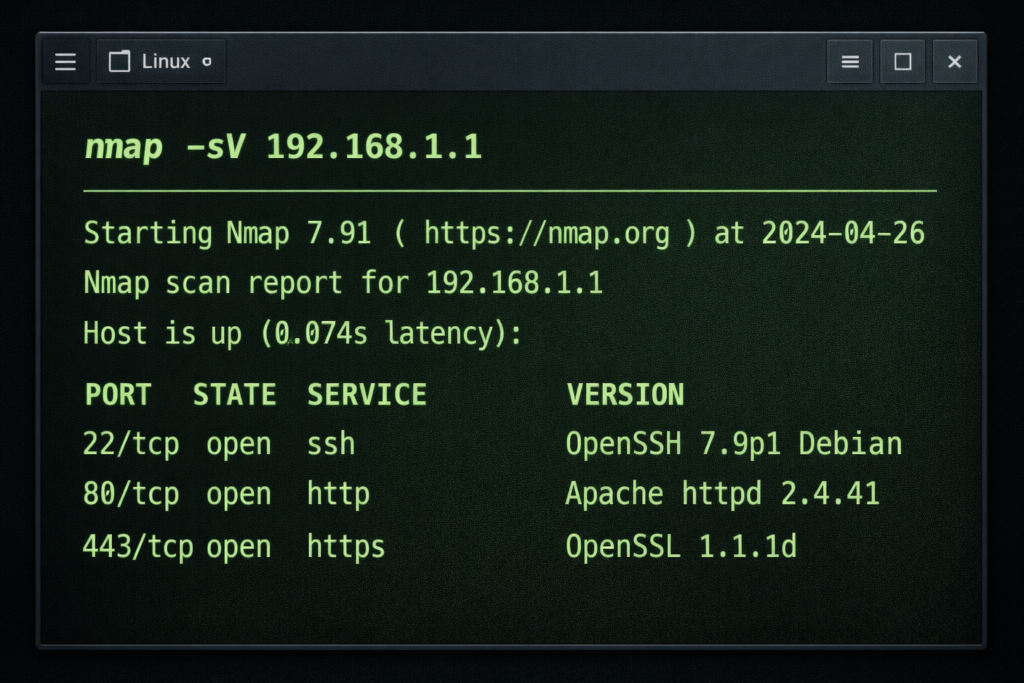
Service Version Detection (-sV)
nmap -sV scanme.nmap.org
Ye running service ka version batata hai.
Example:
80/tcp open http Apache 2.4.41
Version detection vulnerability assessment me helpful hota hai.
OS Detection (-O)
sudo nmap -O scanme.nmap.org
Ye target system ka operating system guess karta hai.
Note: Iske liye sudo required hota hai.
Aggressive Scan (-A)
sudo nmap -A scanme.nmap.org
Ye detailed scan karta hai. Isme include hota hai:
- OS detection
- Version detection
- Script scanning
- Traceroute
Beginners ke liye powerful demo scan hai.
Nmap Scripting Engine (NSE) Kya Hota Hai?
Nmap me ek powerful feature hota hai jise Nmap Scripting Engine (NSE) kehte hain.
Ye scripts use karta hai:
- Vulnerability detection ke liye
- Service enumeration ke liye
- Information gathering ke liye
Example Command:
nmap --script=vuln scanme.nmap.org
Note: Scripts ko sirf authorized systems par hi use karein.
Ye feature advanced level me bahut powerful hota hai.
Port Specific Scan (-p)
nmap -p 80 scanme.nmap.org
Sirf specific port scan karega.
Multiple ports:
nmap -p 21,22,80 scanme.nmap.org
TCP vs UDP Scan
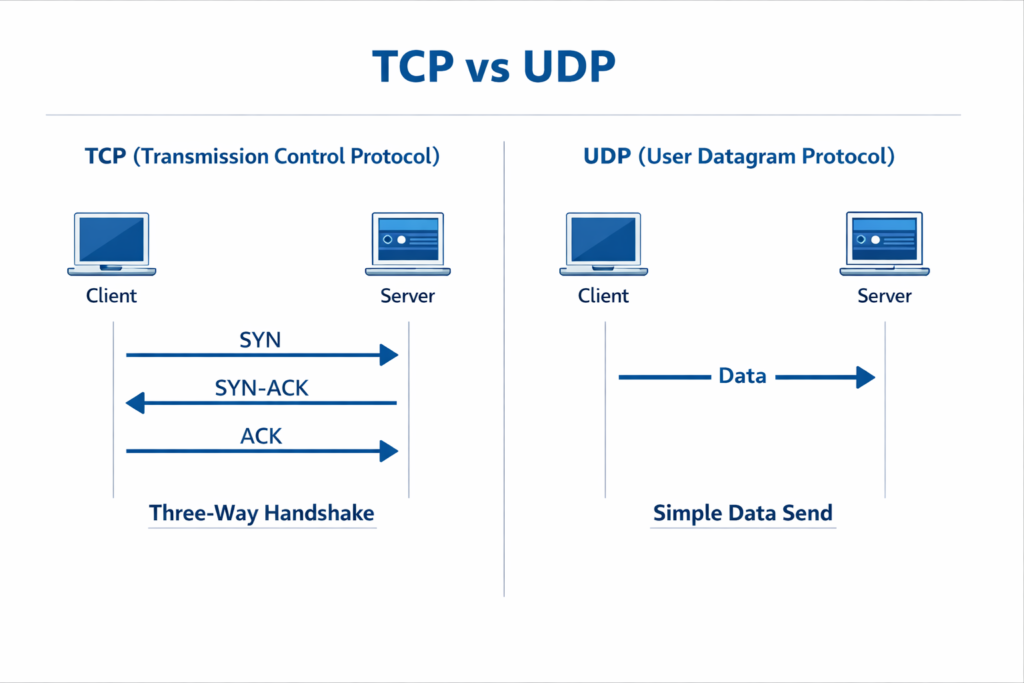
TCP Scan
- Reliable
- Handshake process hota hai
UDP Scan
- Faster
- Less reliable
- Detect karna difficult hota hai
UDP scan command:
sudo nmap -sU scanme.nmap.org
Beginners Ke Liye Recommended Practice Order
Agar aap Nmap properly seekhna chahte ho, to ye order follow karo:
- Basic scan
- Fast scan
- Version detection
- OS detection
- Aggressive scan
Step-by-step approach best hota hai.
Safe Practice Environment
Important Rule:
Kabhi bhi random websites ya unknown servers ko scan mat karo.
Safe Options:
- scanme.nmap.org
- Apna local network
- Virtual machines (VirtualBox, VMware)
- Legal lab environments
Ethical hacking me permission sabse important hoti hai.
Common Mistakes Jo Beginners Karte Hain
- Bina permission scan karna
- sudo use karna bhool jana
- Wrong target dal dena
- Output samjhe bina next command run karna
- Direct aggressive scan start kar dena
Best strategy:
Slow practice + Output understanding.
Pro Tips for Beginners
Agar aap Nmap me fast improve karna chahte ho:
- Daily 10–15 minute practice karo
- Pehle output samjho
- Commands ratne ki jagah use karo
- Apne notes banao
- Safe targets par practice karo
- Screenshots save karo
Consistency se skill fast improve hoti hai.
Real-World Scenario Samjho
Maan lo aap ek company me security intern ho.
Aapko bola gaya:
“Check karo kaun se ports open hain.”
Aap kya karoge?
- Basic scan
- Version detection
- OS detection
- Open services ka analysis
Ye pura process reconnaissance phase ka part hota hai.
Important Nmap Commands Summary
| Command | Purpose |
|---|---|
| nmap target | Basic scan |
| nmap -F target | Fast scan |
| nmap -sS target | SYN scan |
| nmap -sT target | Connect scan |
| nmap -sV target | Version detection |
| nmap -O target | OS detection |
| nmap -A target | Aggressive scan |
| nmap -p 80 target | Specific port |
Ye table beginners ke liye quick revision help karega.
Official documentation ke liye Nmap ki website visit karein.
Frequently Asked Questions (FAQs)
Q1: Kya Nmap free hai?
Haan, Nmap completely free aur open-source tool hai.
Q2: Kya Nmap illegal hai?
Nahi. Tool legal hai. Illegal tab hota hai jab bina permission kisi system ko scan kiya jaye.
Q3: Beginner ko sabse pehle kaunsa scan seekhna chahiye?
Basic scan:
nmap scanme.nmap.org
Q4: Kya Nmap Windows me bhi chal sakta hai?
Haan, Nmap Windows, Linux aur Mac tino par available hai.
Conclusion
Nmap cyber security aur ethical hacking learning ka ek fundamental tool hai. Agar aap beginner ho, to sabse pehle basic scanning commands par focus karo. Dheere-dheere advanced options explore karo.
Regular practice, output understanding aur safe lab environment me experimentation se aapka network scanning concept strong ho jayega.
Yaad rakhein:
Skill tab aati hai jab aap practice karte ho — sirf padhne se nahi.
What’s Next?
Next Topic:
Nmap Port Scanning Types Explained – Complete Guide
Agar aap cyber security step-by-step seekhna chahte ho to Tech Defances ko regular follow karte raho.
Important Note
Ye content sirf educational purpose aur cyber security awareness ke liye share kiya gaya hai. Bina permission kisi system ya network ko scan karna illegal ho sakta hai. Hamesha ethical tareeke se hi learning karein.



Pingback: Nmap Port Scanning Types in Hindi (2026) - Tech Defances
Pingback: Types of Cyber Attacks Explained in Hindi (Complete Guide for Beginners – 2026) - Tech Defances