Cyber security world me network attacks kaafi common ho gaye hain. Jaise-jaise internet ka use badh raha hai, waise-waise attackers naye methods use karke users aur organizations ko target kar rahe hain. In network based attacks me se ek important attack technique hai ARP Spoofing Attack.
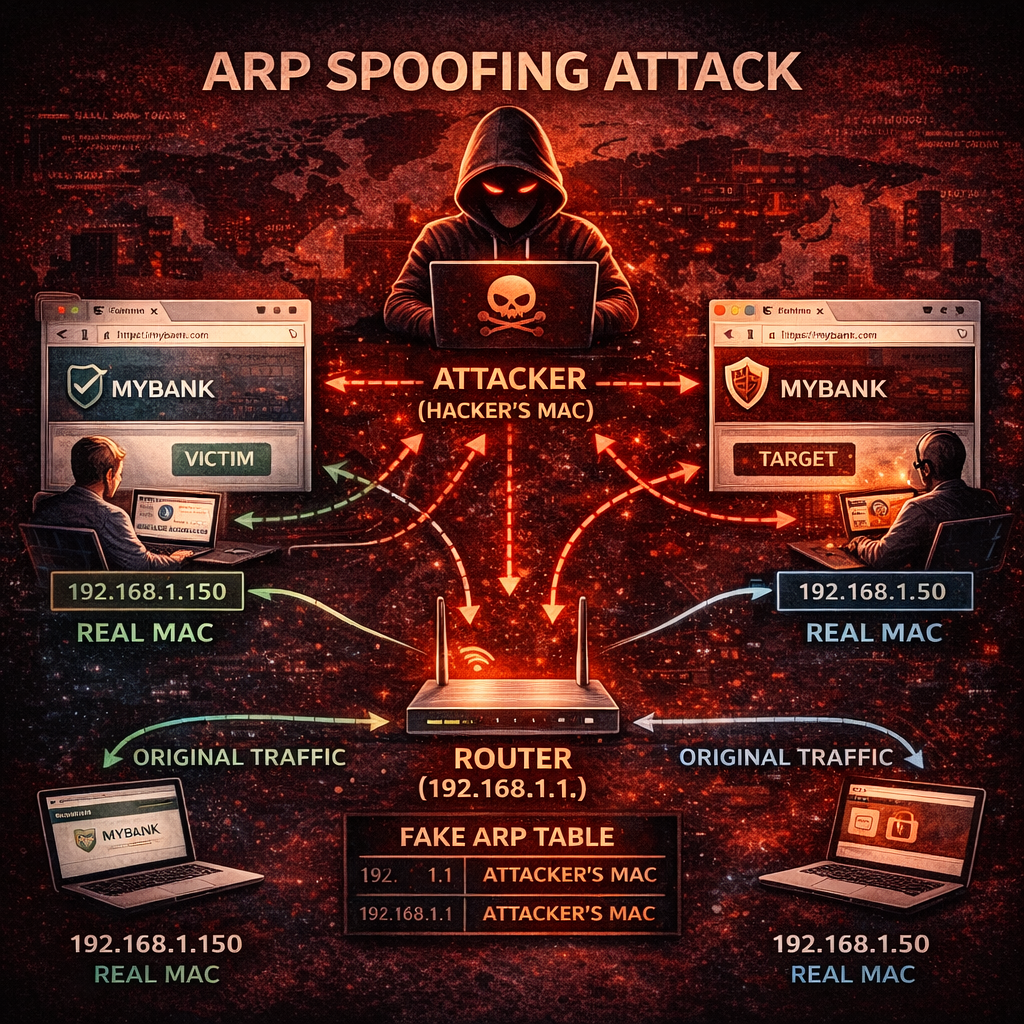
ARP Spoofing ko kai baar ARP Poisoning bhi kaha jata hai. Yeh attack specially local network environments me perform kiya jata hai jahan attacker network traffic ko intercept karne ki koshish karta hai. Kai baar attackers ARP spoofing ka use Man-in-the-Middle (MITM) attack perform karne ke liye karte hain.
Agar kisi network me ARP spoofing attack successful ho jaye to attacker victim ke data ko intercept, monitor ya modify bhi kar sakta hai. Isliye network security ke perspective se ARP spoofing ko samajhna bahut important hai.
Is detailed guide me hum step by step samjhenge:
- ARP kya hota hai
- ARP table kya hoti hai
- ARP spoofing kya hota hai
- ARP spoofing kaise kaam karta hai
- ARP spoofing attack ke steps
- Real world examples
- ARP spoofing aur MITM attack ka relation
- Attack detection methods
- ARP spoofing se kaise bache
- Network security best practices
Yeh guide beginners ke liye simple Hinglish language me likhi gayi hai taaki cyber security concepts easily samajh aaye.
ARP Kya Hota Hai?
ARP ka full form hai Address Resolution Protocol. Yeh ek network protocol hai jo local network me IP address ko MAC address me convert karne ke liye use hota hai.
Jab bhi koi device network par kisi dusre device se communicate karta hai to usse destination device ka MAC address chahiye hota hai. Lekin normally communication IP address ke through hota hai.
Yahan ARP ka role start hota hai.
Example:
Maan lijiye ek computer ko router se connect hona hai. Computer ko router ka IP address pata hai lekin MAC address nahi pata. Is situation me computer ARP request bhejta hai:
“Is IP address ka MAC address kya hai?”
Router ARP reply bhejta hai jisme apna MAC address deta hai.
Is process ko ARP resolution kaha jata hai.
MAC Address Kya Hota Hai?
MAC address ek unique hardware identifier hota hai jo har network device ko assign kiya jata hai.
Example MAC address:
00:1A:2B:3C:4D:5E
Yeh address network card (NIC) se associated hota hai aur local network communication me use hota hai.
IP address logical addressing ke liye hota hai jabki MAC address physical device identification ke liye hota hai.
ARP Table Kya Hoti Hai?
ARP table ek cache hoti hai jo device apne memory me store karta hai. Is table me IP address aur MAC address ka mapping store hota hai.
Example ARP table:
| IP Address | MAC Address |
|---|---|
| 192.168.1.1 | 00:1A:2B:3C |
| 192.168.1.5 | 45:6F:7A:9B |
Iska fayda yeh hota hai ki device ko baar-baar ARP request send nahi karni padti.
Lekin ARP protocol me ek weakness hoti hai: ARP replies verify nahi kiye jate. Isi weakness ka use attacker ARP spoofing attack me karta hai.
ARP Spoofing Kya Hota Hai?
ARP spoofing ek cyber attack technique hai jisme attacker fake ARP messages bhej kar network devices ko confuse karta hai.
Is attack me attacker victim device ko yeh believe karwa deta hai ki attacker ka MAC address actually router ka MAC address hai.
Iska result yeh hota hai ki:
Victim ka network traffic attacker ke system ke through pass hone lagta hai.
Is situation me attacker:
- network traffic monitor kar sakta hai
- sensitive data capture kar sakta hai
- communication modify kar sakta hai
Isi wajah se ARP spoofing ko network poisoning attack bhi kaha jata hai.
ARP Spoofing Attack Kaise Kaam Karta Hai?
ARP spoofing attack ek local network attack hota hai aur generally LAN environment me perform kiya jata hai.
Is attack ka basic concept yeh hai ki attacker network me fake ARP replies bhejta hai.
Step by step process kuch is tarah hota hai:
Step 1 – Network Access
Sabse pehle attacker ko same network par access chahiye hota hai.
Example:
- Public WiFi
- Office network
- Local LAN
Step 2 – ARP Messages Send Karna
Attacker fake ARP replies send karta hai jisme wo apne MAC address ko router ka MAC address batata hai.
Step 3 – ARP Table Poisoning
Victim device ARP table update kar leta hai aur router ke MAC address ki jagah attacker ka MAC address store ho jata hai.
Step 4 – Traffic Redirection
Ab victim ka network traffic attacker ke system ke through route hone lagta hai.
Step 5 – Data Interception
Attacker victim ke data ko monitor, capture ya modify kar sakta hai.
Isi process ko ARP spoofing attack kaha jata hai.
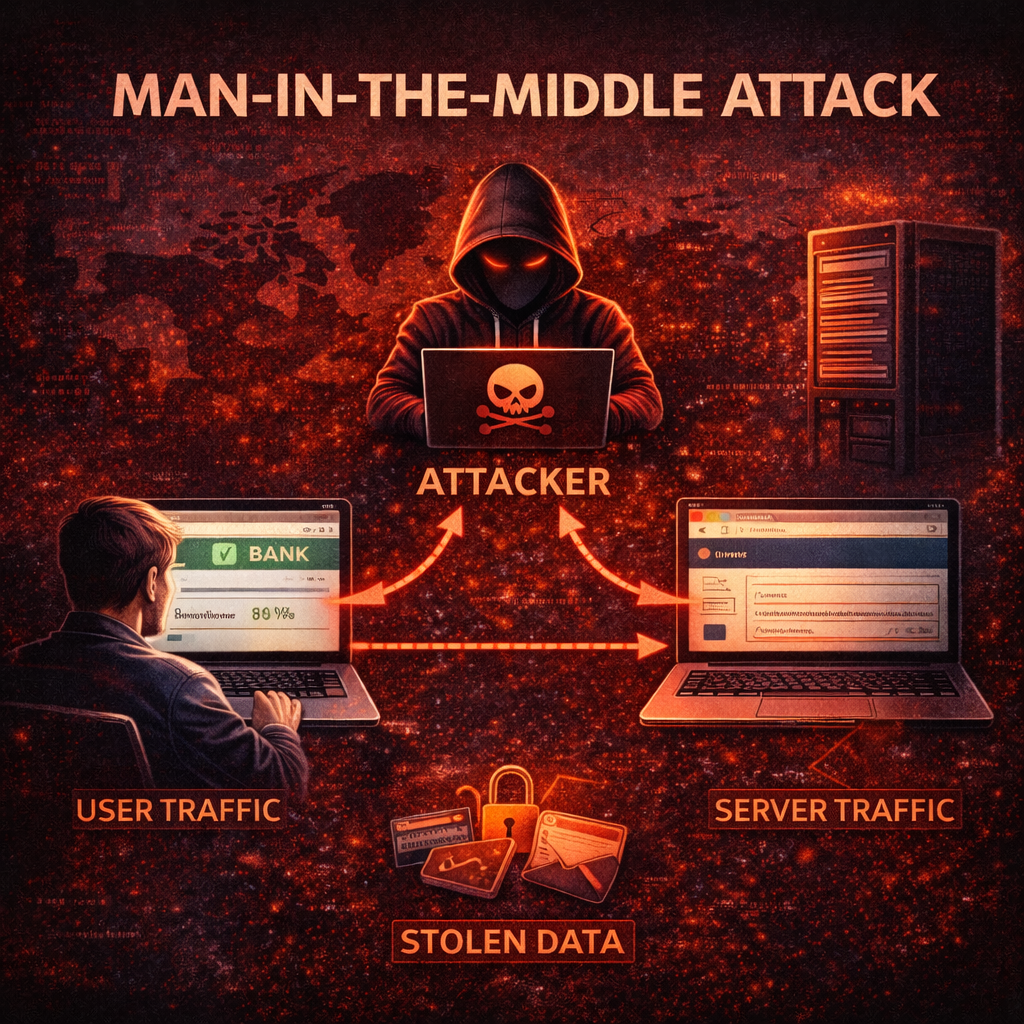
ARP Spoofing Aur MITM Attack Ka Relation
ARP spoofing ka use aksar Man-in-the-Middle attack perform karne ke liye kiya jata hai.
MITM attack me attacker do parties ke beech communication intercept karta hai.
Example:
User ↔ Attacker ↔ Router
User ko lagta hai wo directly router se communicate kar raha hai.
Router ko lagta hai wo user se communicate kar raha hai.
Lekin actually beech me attacker communication ko intercept kar raha hota hai.
Isi wajah se ARP spoofing MITM attack ka ek common technique hai.
Real World ARP Spoofing Example
Maan lijiye ek coffee shop me free WiFi available hai.
Ek attacker bhi us network par connected hai.
Attacker ARP spoofing tool use karta hai.
Victim user jab internet use karta hai to uska traffic attacker ke system ke through pass hone lagta hai.
Ab attacker:
- victim ke login credentials capture kar sakta hai
- websites ke data sniff kar sakta hai
- session cookies steal kar sakta hai
Agar victim unsecured website open karta hai to attacker easily information capture kar sakta hai.
ARP Spoofing Attack Ke Tools
Cyber security testing me kuch tools ARP spoofing ke liye use kiye jate hain.
Example tools:
- Ettercap
- Cain & Abel
- Bettercap
- Dsniff
Yeh tools network traffic sniff karne aur ARP poisoning perform karne ke liye use kiye jate hain.
Ethical hackers in tools ka use penetration testing aur security testing ke liye karte hain.
Unauthorized use illegal ho sakta hai.
ARP Spoofing Attack Ke Risks
Agar ARP spoofing attack successful ho jaye to network security compromise ho sakti hai.
Possible risks:
- Data interception
- Password stealing
- Session hijacking
- Network traffic monitoring
- Malware injection
Corporate networks me ARP spoofing se serious data breaches ho sakte hain.
ARP Spoofing Attack Kaise Detect Kare
ARP spoofing detect karna thoda challenging ho sakta hai lekin kuch techniques use ki ja sakti hain.
1. Network Monitoring
Network administrators unusual traffic patterns detect kar sakte hain.
2. ARP Table Inspection
Agar ek hi MAC address multiple IP addresses ke liye appear ho raha hai to suspicious ho sakta hai.
3. Packet Analysis
Tools jaise Wireshark network packets analyze karne me help karte hain.
4. Intrusion Detection Systems
IDS systems suspicious ARP activity detect kar sakte hain.
ARP Spoofing Se Kaise Bache
Network security improve karne ke liye kuch preventive measures follow karna zaruri hai.
1. Static ARP Entries
Network devices me static ARP entries configure karne se ARP poisoning attacks reduce ho sakte hain.
2. Secure Network Switches
Managed switches me Dynamic ARP Inspection (DAI) feature hota hai jo fake ARP packets detect kar sakta hai.
3. Encryption Use Kare
HTTPS aur VPN encryption use karne se attacker ko data read karna mushkil ho jata hai.
4. Network Segmentation
Network ko multiple segments me divide karne se attacks ka impact reduce hota hai.
5. Secure WiFi Networks
Public WiFi networks avoid karna better hota hai.
6. Regular Security Audits
Organizations ko regular network security testing karni chahiye.
Cyber Security Students Ke Liye Important Advice
Agar aap cyber security ya ethical hacking field me interested ho to ARP spoofing ka concept samajhna important hai.
Lekin:
- Unauthorized networks par testing illegal hai
- Hamesha lab environment use kare
- Virtual machines aur test networks par practice kare
Responsible learning cyber security field me bahut important hai.
Legal Warning
Cyber attacks perform karna illegal ho sakta hai.
India me IT Act 2000 ke under unauthorized network access punishable offense hai.
Cyber security knowledge ka misuse karna legal problems create kar sakta hai.
Isliye cyber security concepts ko sirf educational aur defensive purpose ke liye use karna chahiye.
Conclusion
ARP spoofing ek dangerous network attack technique hai jisme attacker fake ARP messages bhej kar network traffic ko intercept karta hai.
Is attack ka use aksar Man-in-the-Middle attacks perform karne ke liye kiya jata hai.
Agar network properly secure na ho to attackers sensitive data capture kar sakte hain.
Network security improve karne ke liye organizations aur users ko strong security practices follow karni chahiye.
Important safety measures:
- Secure network infrastructure
- Encryption use kare
- Network monitoring implement kare
- Security awareness maintain kare
Cyber security me awareness aur prevention hi sabse strong defense hai.
What’s Next?
Next Guide:
DNS Spoofing Attack Kya Hota Hai? Working, Real Examples aur Prevention Guide (2026)
Important Note
Ye content sirf educational purpose aur cyber security awareness ke liye share kiya gaya hai. Bina permission kisi website ya system par testing karna illegal ho sakta hai.